Last time, we discussed the role of a WiFi/Access edge firewall in protecting your network, and how it complements your perimeter firewall. Today, let's talk about how that same firewall actually makes the job of the network architect and manager easier.
保持网络中另一个防火墙配置的配置似乎是对立的,这将节省您的时间,并为更简单,更可扩展的设计提供几分钟,但我将解释一下Aruba的PEF防火墙和相关功能如何才能完成那。
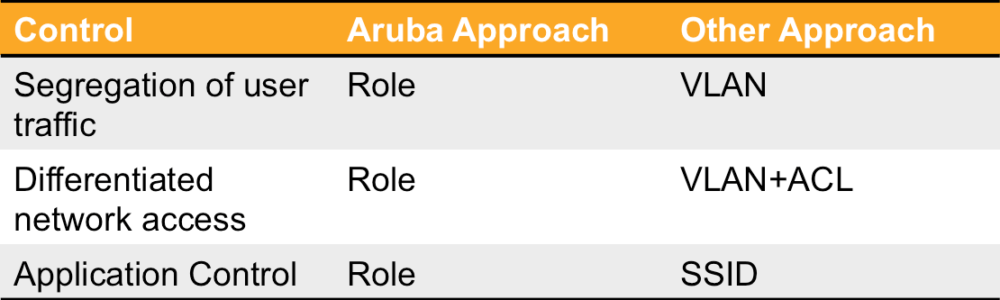
简化访问控制
在我们上次讨论的概念的基础上,让我们假设您至少有限制网络上用户访问的适度需求。这可能很简单,就像为客人提供仅互联网访问权限,或者可以包括对员工BYOD设备的简单控件。无论您的需求如何,让我们看一下替代解决方案。
VLAN和ACL
基于角色的状态访问防火墙的最常见替代方法是将不同的用户映射到不同的虚拟LAN(VLAN)并添加静态访问控制列表的尝试和真实方法,以试图将流量从不应该去的地方放走。该解决方案有一些缺点,使维护更加困难,并减少了努力的安全性。
该解决方案的最大问题是,需要在任何地方提供适当的VLAN,给定类别的用户将连接到网络。这意味着给定的VLAN或具有相同名称/号码的一个,需要在整个网络的整个边缘存在。这提出了一些挑战。第一,必须注意确保这些VLAN到处都有。其次,如果使用完全相同的实际VLAN,那么网络的直径很可能是由从一端到另一端的开关啤酒花的数量定义的 - 将会长大足够大,以至于有可能跨越树的潜力引起网络中断的问题。这是添加了许多扩展名的原因之一,以及为什么这么多供应商开发了自己的方法来循环管理。
当然,安全是另一个问题。几乎所有这些方法都取决于“静态” ACL(单独查看每个数据包,没有状态信息),而不是对用户及其访问权利的持续了解。这种方法对于粗粒访问就可以了,例如阻止所有对特定网络的访问。但是它缺乏完成重要事情的能力,例如将用户的传入和传出会话映射在一起,以便可以安全地将服务器响应发送回客户端。这很大程度上限制了这些控件可以做的事情。
Another drawback of this lack of session awareness is a lack of accountability - that is, logging information. By being user and session aware, Aruba's PEF firewall is able to log who accesses resource when, and from where. It also allows mapping of users to applications, web browsing behavior, and Unified Communications calls. This information can be used for auditing, compliance, and troubleshooting purposes. Add a powerful network management tool like Airwave to the mix, and this data becomes an invaluable tool.
SSID和应用程序控制
如今,普遍的要求是限制允许给定用户社区使用的应用程序,或限制允许使用的带宽量。典型的动机是执行可接受的用户政策,并担心保持关键应用程序的最佳性能。
Doing the deep packet inspection required to make this application identification can sometimes turn out to be the easy part of the exercise. How do we layer this control onto our existing set of controls - VLANs and ACLs? Maybe make a decision based on SSIDs instead? That's the one!
认真地说,这在边缘创造了另一组配置复杂性。现在,您需要担心给定用户连接到的SSID是什么(只有客户端可以控制的东西),然后将其映射到哪个VLAN以及分配给该VLAN的ACL的基础集。需要更改某些东西,您需要查看所有这些领域,以确保更改具有理想的影响。
Obviously, the best approach to adding application visibility and control to your network would be to add these controls to the existing concepts already established with the access firewall. Adding stateful Application ACLs to the existing roles accomplishes this in an Aruba network without the need for new SSIDs.
动态下载的ACL
由于这两个巨大的缺点,一些供应商一直在扩展其安全模型以包括动态访问控件。在这种情况下,用户组或用户的角色在用户登录时触发一组访问控制列表的下载。跨越我们讨论的树问题。
However, there are two problems with this approach. Firstly, the ACLs are still stateless. Secondly, implementing this type of an architecture is often quite complicated. Typically, a complex network management tool is required. This tool often has several required components that must be installed and configured correctly in order to pull this off. Secondly, the capability to receive the ACLs, and the appropriate configuration, must be present ubiquitously throughout the switched edge network in order for this approach to work.
简化网络设计,提高可靠性
One of the key elements of Aruba's WiFi architecture is the fact that the traffic from all the Access Points is sent back through the network to the controller via a GRE tunnel. Once in the controller, the firewall is the next step for all the traffic. This approach dramatically simplifies VLAN management and scalability.
在阿鲁巴岛架构中,美联社需要一个当地的IPaddress at the edge. This is generally done via DHCP. This is the ONLY IP address that is consumed on the local VLANs. Instead of mapping the users to local VLANs, all user traffic is sourced from a VLAN that resides on the controller. This means that no VLANs need to be plumbed from the edge to the distribution layer for the client traffic. Furthermore, the controller can assign a VLAN to the user via a "VLAN pool" - a large collection of VLANs. This makes it very simple to add additional VLANs as the device community as the edge grows and IP addresses are depleted. Eliminating the proliferation of VLANs throughout the access layer reduces the complexity, configuration time, and significantly enhances the reliability of the Spanning Tree infrastructure at the edge.






